Best Practices for Handling API Rate Limits and Retries Across Multiple Third-Party APIs
Learn proven patterns for handling API rate limits and retries across dozens of SaaS APIs - from exponential backoff with jitter to normalizing inconsistent provider headers at scale.
If your B2B SaaS product integrates with even five third-party APIs, you've already been bitten by rate limits. Maybe you've seen a sync job silently drop records because Salesforce returned a 429 your code didn't handle. Or your Jira integration brought down a customer's entire data pipeline because a naive retry loop hammered an already-throttled endpoint. What starts as a simple script to pull data from a CRM to build the integrations your sales team actually asks for inevitably mutates into a complex distributed system where third-party API rate limits are not minor annoyances - they are hard boundaries that can severely destabilize your own application if handled incorrectly.
This post covers the real-world patterns - and the hard trade-offs - for handling API rate limits and retries at scale across multiple providers.
The Hidden Cost of Ignoring API Rate Limits
Most teams treat rate limiting as a "we'll handle it later" problem. That's a mistake with a measurable price tag.
The blast radius of a poorly handled rate limit extends far beyond a single dropped request. When a retry loop doesn't respect backoff, it hammers the provider harder, which extends the rate limit window, which triggers more retries. This aggressively consumes CPU cycles, holds open database connections, and exhausts memory. Within minutes, your own background workers crash. A failure in a downstream integration has now taken down your core product.
The financial risk is equally severe. One developer publicly documented burning through $40,000 in cloud costs from a single incident where a bypassable rate limiter failed to stop a bot attack, triggering massive backend processing spikes. The root cause wasn't a sophisticated exploit - it was an X-Forwarded-For header their rate limiter trusted blindly.
Beyond compute waste, there is the security and reliability angle. According to Orbilon Technologies, the average API security breach or failure costs $4.5 million per incident, with 83% of data breaches involving APIs directly. When you multiply this risk across dozens of third-party integrations, the complexity compounds. You're not just building features; you're managing a fragile ecosystem where you have zero control over the downstream nodes.
And in integration-heavy architectures, the risk gets worse. You're not just making API calls for your own service - you're making them on behalf of dozens or hundreds of customer accounts, often against the same provider. A single misbehaving sync job for one customer can burn through the shared rate limit quota for every other customer using the same integration. That's the kind of incident that gets engineering leaders pulled into executive meetings.
Understanding the HTTP 429 "Too Many Requests" Standard
Before architecting a solution, we need to establish the baseline standard. HTTP 429 Too Many Requests is the status code that tells a client it has exceeded the allowed request rate. It was formally defined in RFC 6585, published in April 2012.
Before RFC 6585, APIs improvised. Twitter famously used 420 Enhance Your Calm as a custom rate limit code, forcing developers to write platform-specific error handlers. Some providers still return 403 Forbidden or - worse - 200 OK with an error buried in the response body. (We wrote about these patterns in depth in our post on how third-party APIs can't get their errors straight.)
The Retry-After Header
When a server returns a 429, it is explicitly telling the client to stop sending requests. Simply stopping is not enough - the client needs to know exactly when it is safe to resume traffic.
The Retry-After header is the companion to 429. As confirmed by MDN Web Docs, the Retry-After response header indicates how long the user agent should wait before making a follow-up request. It accepts two formats:
- Seconds:
Retry-After: 60(wait 60 seconds) - HTTP-date:
Retry-After: Wed, 21 Oct 2025 07:28:00 GMT(wait until this time)
A properly formatted 429 response looks like this:
HTTP/1.1 429 Too Many Requests
Retry-After: 60
X-RateLimit-Limit: 100
X-RateLimit-Remaining: 0
X-RateLimit-Reset: 1699564800
Content-Type: application/json
{"error": "rate_limit_exceeded", "message": "Limit of 100 requests per minute exceeded"}The Dirty Secret: Nobody Implements This the Same Way
The standard exists on paper. The problem is that every SaaS API interprets it differently, and the differences aren't cosmetic:
| Provider Behavior | What Your Code Expects | What Actually Happens |
|---|---|---|
Standard 429 + Retry-After |
Parse header, wait, retry | Works as designed |
429 without Retry-After |
Fall back to exponential backoff | You're guessing how long to wait |
200 OK with error in body |
Success path triggers | Silent data loss |
403 used as rate limit |
Auth failure handling kicks in | Unnecessary token refresh |
Custom header like X-RateLimit-Reset |
Standard Retry-After |
Missed entirely unless you write custom parsing |
Many APIs return headers like X-RateLimit-Limit, X-RateLimit-Remaining, and X-RateLimit-Reset to make remaining quota visible. But the header names, value formats, and reset semantics vary wildly between providers. GitHub uses X-RateLimit-Reset as a Unix timestamp. Shopify uses Retry-After in seconds. HubSpot includes a X-HubSpot-RateLimit-Daily-Remaining header. When you're integrating with 20+ APIs, this inconsistency is where the real engineering time goes.
Best Practices for Handling API Rate Limits and Retries
Here are the patterns that actually work in production when you're dealing with multiple providers simultaneously.
1. Always Implement Exponential Backoff with Jitter
A naive retry loop waits a fixed amount of time (e.g., 5 seconds) and tries again. If a third-party API experiences a brief outage and 1,000 of your background jobs hit a 429 simultaneously, a fixed delay means all 1,000 jobs will retry at the exact same millisecond 5 seconds later.
This creates a thundering herd - a massive, synchronized spike in traffic that will instantly crush the recovering server, resulting in more 429s or 503s.
Exponential backoff progressively increases the wait time between retries: 1s, 2s, 4s, 8s, and so on. But on its own, it's not enough. If multiple clients experience failures simultaneously, they might all retry at the same time, creating synchronized waves of traffic.
Jitter - a random offset added to each retry delay - solves this. Instead of all clients retrying after exactly 2 seconds, some might wait 1.7 seconds, others 2.3 seconds, spreading out the load.
sequenceDiagram
participant Clients
participant API
Clients->>API: 100 concurrent requests
API-->>Clients: 429 Too Many Requests
Note over Clients: Without Jitter:<br>All wait exactly 5.0s
Clients->>API: 100 concurrent requests at T+5s
API-->>Clients: 429 Too Many Requests
Note over Clients: With Jitter:<br>Wait 5.0s + random(0, 2s)
Clients->>API: 20 requests at T+5.1s
API-->>Clients: 200 OK
Clients->>API: 30 requests at T+5.6s
API-->>Clients: 200 OKHere's a production-grade implementation in TypeScript:
function retryWithBackoff<T>(
fn: () => Promise<T>,
options: {
maxRetries: number;
baseDelayMs: number;
maxDelayMs: number;
retryableStatuses: number[];
}
): Promise<T> {
const { maxRetries, baseDelayMs, maxDelayMs, retryableStatuses } = options;
async function attempt(retryCount: number): Promise<T> {
try {
return await fn();
} catch (error: any) {
if (
retryCount >= maxRetries ||
!retryableStatuses.includes(error.status)
) {
throw error;
}
// Always prefer the server's Retry-After header over your own backoff
const retryAfter = parseRetryAfter(error.headers?.get('retry-after'));
// Exponential backoff with full jitter
const exponentialDelay = baseDelayMs * Math.pow(2, retryCount);
const cappedDelay = Math.min(exponentialDelay, maxDelayMs);
const jitteredDelay = Math.random() * cappedDelay;
const waitMs = retryAfter ? retryAfter * 1000 : jitteredDelay;
await sleep(waitMs);
return attempt(retryCount + 1);
}
}
return attempt(0);
}The key detail: always prefer the server's Retry-After header over your own backoff calculation. The server knows its own recovery timeline better than your client does.
2. Respect Layered Rate Limiters
Enterprise APIs do not use a single, monolithic rate limit. They use multiple layers of limiters to protect different parts of their infrastructure. Stripe, for instance, explicitly documents their approach, which utilizes token buckets for overall request rates and separate limiters for concurrent requests. They run at least four different types of limiters in production.
- Request Rate Limiters: Cap the total number of API calls over a time period (e.g., 100 per minute).
- Concurrent Limiters: Cap the number of simultaneous active connections (e.g., maximum 20 at once) to protect CPU-intensive endpoints.
If you send 50 slow, complex requests at once, you will hit the concurrent limit and receive a 429, even if your token bucket is full. Your architecture must be prepared to handle 429s at any time, regardless of what your internal client-side rate limit trackers predict.
3. Use Circuit Breakers to Stop the Bleeding
Retries handle transient failures. Circuit breakers handle sustained failures. Sometimes an API isn't just rate limiting you; it's completely degraded. If you receive continuous 429s or 5xx errors, your system should "trip" a circuit breaker.
The three states are simple:
- Closed (normal): Requests flow through.
- Open (tripped): All requests fail immediately without hitting the provider. This prevents your background workers from filling up with doomed tasks and exhausting your system memory.
- Half-open (testing): A single request is let through to probe recovery.
Without a circuit breaker, a rate-limited integration can monopolize your worker threads, starving healthy integrations of resources.
4. Track Rate Limit State Proactively
Don't wait for a 429 to start throttling. Monitor rate-limit headers before you hit the ceiling. Many APIs include X-RateLimit-Remaining headers on every response - not just error responses.
This means parsing and storing rate limit state on every response and using that state to pre-emptively throttle outgoing requests. This is especially critical when multiple internal services share the same API credentials. If service A burns 90% of the quota, service B shouldn't have to discover that by getting a 429.
5. Make Operations Idempotent
Retrying a GET request is inherently safe. Retrying a POST request that creates a new record is highly dangerous. If your initial request timed out, but the third-party server actually processed it, a blind retry will create a duplicate record.
Always use idempotency keys when interacting with APIs that support them. If you receive a 429 or a 502 on a state-mutating request, the idempotency key ensures that the eventual successful retry does not result in corrupted or duplicated data. Without idempotency, you'll spend more time deduplicating than you saved by retrying.
6. Separate Rate Limit Budgets Per Customer Account
If your platform makes API calls on behalf of multiple customers against the same provider, you need per-account rate tracking. One customer's aggressive sync schedule shouldn't exhaust the rate limit for everyone else. This requires a shared rate limit state store (typically Redis) that all workers consult before making requests. Distributed rate limit tracking is the only way to prevent one service from burning the quota for another.
The Nightmare of Normalizing Rate Limits Across 100+ APIs
The best practices above work great for one or two integrations. They become an engineering quagmire when you're building a platform that connects to dozens of third-party APIs.
The real problem: every SaaS API implements rate limiting differently, and the differences aren't just cosmetic.
Consider what you'd need to handle for just three popular APIs:
- Salesforce: Returns
429with aRetry-Afterheader in seconds, but also enforces a 24-hour rolling limit that resets at midnight UTC. Exceeding the daily limit returns a different error body format. - HubSpot: Uses both per-second and daily rate limits with
X-HubSpot-RateLimit-*custom headers. The limit varies by OAuth app tier. - Jira: Rate limits are undocumented for Cloud, return
429withRetry-After, but theX-RateLimit-Resetvalue is a Unix timestamp (not seconds-from-now).
The Reality of Third-Party APIs Standard HTTP 429 responses are a myth in the wild. You will encounter edge cases that directly violate standard HTTP conventions.
- The 200 OK Error Trap: GraphQL APIs are notorious for this. Even when a query fails entirely due to a rate limit, GraphQL endpoints almost always return a
200 OKstatus. The actual error is hidden inside anerrorsarray in the response body. Your standard HTTP client will see a 200 and assume success, completely bypassing your retry logic. - Semantically Incorrect Status Codes: Freshdesk returns a
429 Too Many Requestswhen a customer's subscription plan does not include API access. A real rate limit returns a 429 with a Retry-After header. Without that header, the error actually means402 Payment Required, forcing your code to guess the context. - Proprietary Headers: Instead of the standard
Retry-Afterheader, APIs invent their own. SometimesX-RateLimit-Resetis a Unix timestamp in milliseconds. Sometimes it is in seconds. Sometimes it is a string representation of a date.
Now multiply these quirks by 50 or 100 integrations. Your options are:
-
Write custom rate limit handling per integration. This is what most teams do first. It works until it doesn't - specifically, around the 10-15 integration threshold where the true cost of building integrations in-house starts to overwhelm feature development.
-
Build an internal abstraction layer. Better, but you're now maintaining a mini-platform that needs to understand every provider's rate limit semantics, header formats, and edge cases. You've traded integration debt for infrastructure debt.
-
Use a unified API layer that normalizes rate limits at the platform level. This pushes the normalization complexity to a purpose-built system.
The real cost isn't writing the initial retry logic. It's maintaining it. API providers change rate limit policies without notice. They add new header formats. They change the semantics of existing headers. Each change is a potential production incident for your integration layer.
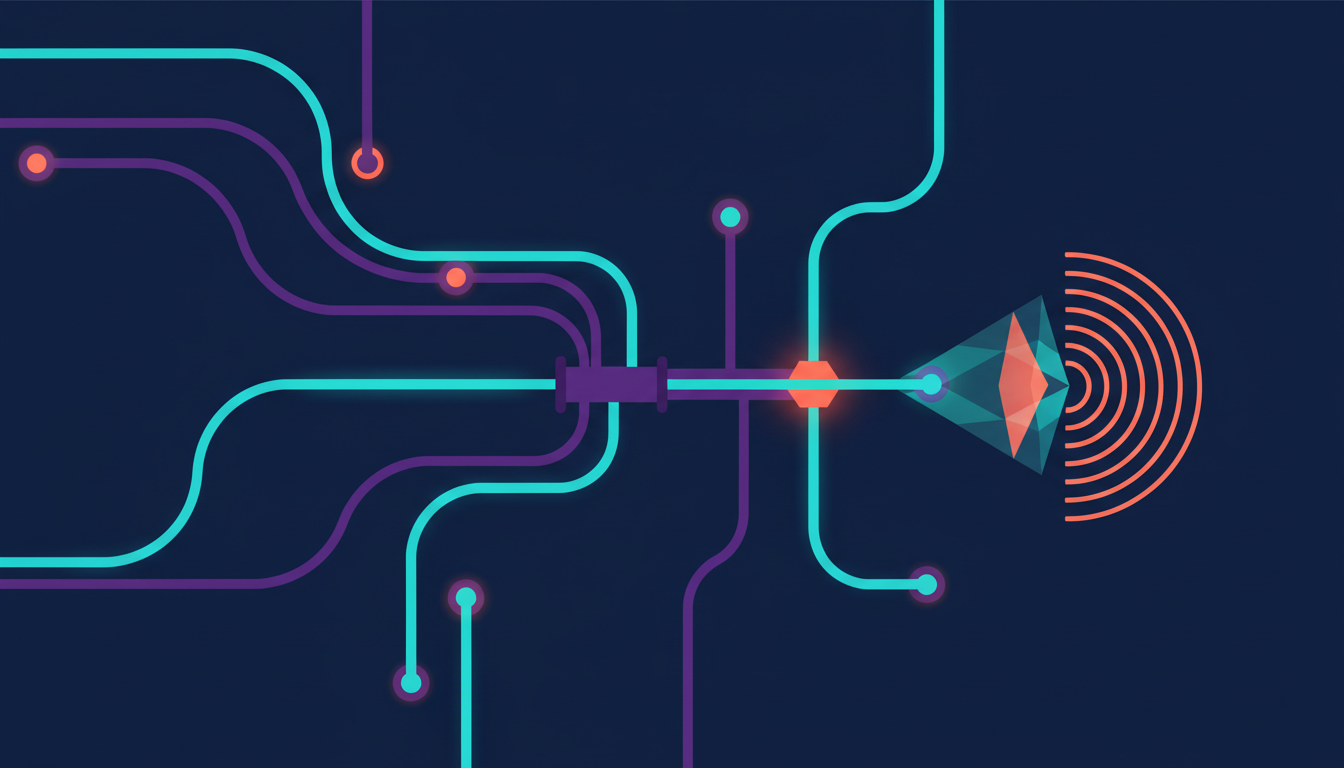
How Truto Standardizes Rate Limits and Retries Automatically
This is the specific problem Truto's architecture was designed to solve. Truto handles rate limit detection and retry logic at the platform level, meaning developers do not have to write custom backoff loops for dozens of different APIs.
Truto achieves this with zero integration-specific code. Instead of writing custom scripts for every provider, Truto uses a generic execution pipeline driven by JSON configuration.
Single Config-Driven Rate Limit Detection
Every integration in Truto includes a rate limit configuration that defines three things using powerful JSONata expressions:
-
How to detect a rate limit - An expression that evaluates the response status and body to determine if the request was rate-limited. For APIs that return
429, this is trivial. For APIs that signal rate limits through200 OKresponses with error bodies or non-standard status codes, the expression handles the translation. -
How to extract the retry delay - An expression that reads the provider's specific "when to retry" signal (whether that's
Retry-After,X-RateLimit-Reset, a Unix timestamp, or a custom header) and converts it to a standard number of seconds. -
How to extract rate limit metadata - An expression that maps the provider's limit/remaining/reset headers into standardized response headers.
Here's how this configuration looks conceptually:
rate_limit: {
is_rate_limited: "$status = 429 or $contains($body.error.message, 'rate limit')",
retry_after_header_expression: "$exists($headers.'x-ratelimit-reset') ? $number($headers.'x-ratelimit-reset') - $millis()/1000 : 60",
rate_limit_header_expression: "{ 'limit': $headers.'x-ratelimit-limit', 'remaining': $headers.'x-ratelimit-remaining' }"
}flowchart LR
A["Your App"] -->|Single API call| B["Truto Unified API"]
B --> C{"Rate limit<br>config"}
C -->|JSONata expr| D["Salesforce<br>429 + Retry-After"]
C -->|JSONata expr| E["Slack<br>200 + ok:false"]
C -->|JSONata expr| F["Custom API<br>X-RateLimit-Reset"]
D --> G["Standardized<br>429 + Retry-After<br>+ ratelimit-*"]
E --> G
F --> G
G --> AWhat Your Client Code Actually Sees
Regardless of whether the upstream API returns a standard 429, a 200 with an error body, or a 403 being misused as a rate limit signal, Truto normalizes the response consistently:
| Your Client Receives | Description |
|---|---|
429 status code |
Always a standard HTTP 429 |
Retry-After header |
Seconds until retry, derived from whatever the provider sent |
ratelimit-limit header |
Total allowed requests per window |
ratelimit-remaining header |
Remaining requests in current window |
ratelimit-reset header |
When the window resets |
These standardized headers appear on both error and success responses, so your client can proactively track rate limit state without waiting for a 429. When Truto detects a rate limit - even if the upstream API hid it inside a 200 OK GraphQL response - it normalizes the HTTP status to 429 and appends truto_error_insight.rate_limit_error to the payload. Your client code only ever has to look for one standard error format, completely decoupling your application logic from the quirks of the underlying provider.
The practical impact: you write your retry logic exactly once. One backoff strategy. One set of header parsing. One circuit breaker configuration. It works across Salesforce, HubSpot, Jira, BambooHR, QuickBooks, and every other integration Truto supports.
Built-in Queue Retries for Webhooks
Rate limits don't just affect outbound requests; they affect inbound asynchronous data too, which is a common pain point when handling real-time data sync from legacy APIs. If your internal systems are overwhelmed and start rejecting incoming webhooks, data is lost permanently.
For third-party webhooks, Truto uses a queue-based architecture with built-in exponential backoff. Failed deliveries are retried automatically, and payloads are stored in object storage before queue processing, so data isn't lost even if retries are needed. If persistent failures occur, health monitoring can auto-disable the webhook endpoint. (We covered this pattern in detail in designing reliable webhooks.)
The Honest Trade-offs
A unified API isn't a silver bullet. There are real trade-offs you should understand:
- You're adding a hop. Your requests go through Truto's infrastructure before hitting the provider. That adds latency (typically single-digit milliseconds, but it's not zero).
- Provider-specific optimizations are harder. If Salesforce's composite API lets you batch 25 requests into one call, you lose that advantage when working through a unified model. (Truto's proxy API mode can help here, but it requires you to think provider-specifically.)
- You're trusting the normalization layer. If a JSONata expression has a bug, the rate limit signal could be lost. Truto's architecture mitigates this with fallback behavior - if no custom detection expression exists, standard
429detection still works - but it's a dependency you should understand.
For rate limit normalization specifically, the architectural fit is strong. But going in clear-eyed about the trade-offs matters.
Building a Rate Limit Strategy That Scales
Whether you build your rate limit handling in-house or use a platform like Truto, the architectural principles stay the same:
-
Centralize rate limit state. Every service making API calls on behalf of your customers should consult a shared state store. Distributed rate limit tracking is the only way to prevent one service from burning the quota for another.
-
Standardize your internal contract. Pick a format -
Retry-Afterin seconds,ratelimit-*headers - and make every integration adapter expose the same interface to your business logic. Don't let provider-specific semantics leak into your core application. -
Monitor rate limit consumption as a first-class metric. Track
ratelimit-remainingacross all integrations. Set alerts at 80% consumption so your team can investigate before customers are affected. -
Test with simulated
429responses. These retry strategies are best validated before release. Tools like Postman let you simulate 429 responses across environments to verify that your client logic behaves correctly under throttling conditions. -
Plan for the long tail. Your first 10 integrations will probably all return
429withRetry-After. Integration number 37 will return200 OKwith{"error": true, "wait_seconds": 30}buried three levels deep in a JSON response. Design your abstraction layer to handle that from day one.
The companies that get this right treat rate limit handling as infrastructure, not a per-integration afterthought. The ones that don't end up with an engineering team that spends more time debugging silent sync failures than building product features.
FAQ
- What is the standard HTTP status code for an API rate limit?
- The universally accepted standard is the HTTP 429 "Too Many Requests" status code, defined by RFC 6585. It is typically accompanied by a Retry-After header indicating when the client can safely resume requests.
- Why is exponential backoff with jitter better than a fixed retry delay?
- A fixed delay can cause a "thundering herd" problem where hundreds of failed requests retry at the exact same millisecond, crashing the recovering server. Exponential backoff progressively doubles the wait time, and jitter adds a random offset to each delay so that retries are spread out organically over time.
- Why do different APIs handle rate limits differently?
- There is no enforced standard for how rate limit metadata is communicated. Some APIs use Retry-After headers, others use custom X-RateLimit-* headers, and some return 200 OK with error details in the body. This inconsistency forces developers to write custom parsing logic per provider.
- How do you prevent one customer's API usage from rate limiting all customers?
- Use per-account rate tracking with a shared state store like Redis. Each customer account should have its own rate limit budget so that one aggressive sync job doesn't exhaust the shared quota for all other customers using the same integration.
- How does Truto handle third-party API rate limits?
- Truto uses JSONata expressions to normalize proprietary rate limit headers and status codes from any third-party API into standard HTTP 429 responses and Retry-After headers. This eliminates the need for integration-specific retry logic across all providers.